7 Steps to Keeping a Connected Home Safe
- By Matt Holden
- Mar 10, 2015
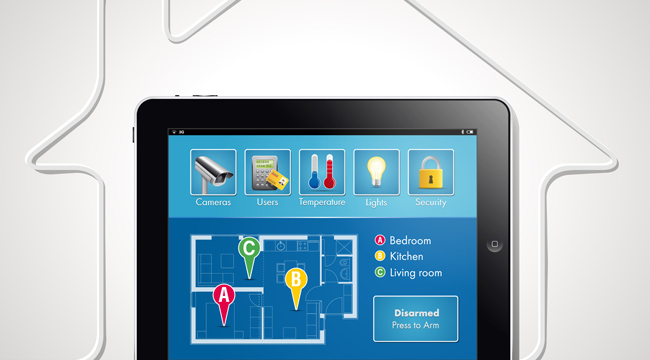
Today, homes are becoming smarter than ever, with security systems, thermostats and even the blinds on a window getting connected through the internet. While convenient, these smart technologies also create vulnerability in your network.
TechHive has posted a list of seven steps you can take to ensure your connected home is safe:
1. Be aware of the data each device can capture
For example, a television that has a front-facing camera could potentially capture footage in your living room without you knowing. Hackers can remotely monitor homes if they are able to break into networked security cameras.
2. Make the most of your devices’ security features
Default configurations on most devices can be found by using a simple Google search, so changing the usernames and passwords right out of the box is a must. Naturally, the stronger the password, the better.
3. Keep your networks separate
While it may seem like a good idea to keep all of your security devices on the same networks as your computer and other systems, this allows hackers access to everything by getting through the network only once. Known as “network segmenting,” most advanced routers can set up multiple networks.
4. Hide your network
It is also possible to configure your Wi-Fi network in a way that will make it invisible to automatic searching. This won’t work against experienced criminals, but it’s at least a step in the right direction.
5. Be careful about who handles your devices
Look out for scammers who offer to fix and improve devices, as well as unauthorized shops that say they can repair it. This is especially true if your device can be access via USB, a common gateway for hacking.
6. Keep an eye on your bills
This is mostly for connected devices that have a smart meter and automatic bill payment set up. In rare cases, a neighbor in an apartment could rewire their own meters to reduce ratings and hack yours to increase them, making the numbers even out for utility companies.
7. Take standard internet precautions
Mostly all smart devices connect via the internet, so be sure not to leave private access on public computers, and make sure your phone has secure passwords and secondary passwords for each individual device you access from it.
About the Author
Matt Holden is an Associate Content Editor for 1105 Media, Inc. He received his MFA and BA in journalism from Ball State University in Muncie, Indiana. He currently writes and edits for Occupational Health & Safety magazine, and Security Today.