
Whether it is water, electricity, gas, oil or even telecommunications and transportation hubs, critical infrastructure facilities present unique challenges for security professionals.
- By Michael Shipley
- Dec 01, 2021
Federal, state and local agencies prioritize robust physical security plans for the nation’s electric power utilities. And they should. Any disruption in service from a primary provider could impact millions of people and businesses over a wide swath of the country.
- By John Nemerofsky
- Dec 03, 2020

Franco Zaro of Valid breaks down new government efforts to establish a 5G security strategy and public paranoia about the wireless infrastructure.
- By Haley Samsel
- Apr 16, 2020

Security is top of mind for consumers around the
world and businesses across industries.
- By Brian Mallari
- Sep 01, 2019

If the Securing Energy Infrastructure Act is signed into law, it will create a working group tasked with isolating the energy grid from attacks using “manual procedures.”
- By Haley Samsel
- Jul 09, 2019

Empresa Eléctrica de Guatemala (EEGSA Group) required a video surveillance system that could digitize the security footage on its substations to help avoid damage to its own infrastructure as well as electrocution hazards for people trying to access these places without warning or authorization.
- By Courtney Pedersen
- Feb 01, 2018

Maintaining the security of our nation’s water supplies is serious business. Attacks from a lone vandal to a team of foreign terrorists could, within hours, result in widespread illness or economic disruption.
- By Bruce Czerwinski
- Jan 01, 2017

Thanks to a number of new technology advancements, power supplies and transmission solutions with network management features are a natural progression for ensuring the reliability of today’s IP-based physical security systems.
- By Ronnie Pennington
- Dec 29, 2016

Most security professionals have acquired important video only to see that the resulting footage is over or under exposed because the camera is unable to adapt to the challenging light environment.
- By Kevin Shen
- Nov 01, 2016

April 28, 2014, stands out in the memory of the residents of northern Mississippi as a violent F4 Tornado left a wake of major damage killing 10 people and injuring more than 80.
- By Peggy Page
- Nov 01, 2016
PVSC has a stated mission of enhancing the viability and environmental health and security of 1.4 million residents in 48 municipalities, an important task that requires maximum security and the ability to surveil operations at all times.
- By Viktoriya Vudmaska
- Oct 03, 2016
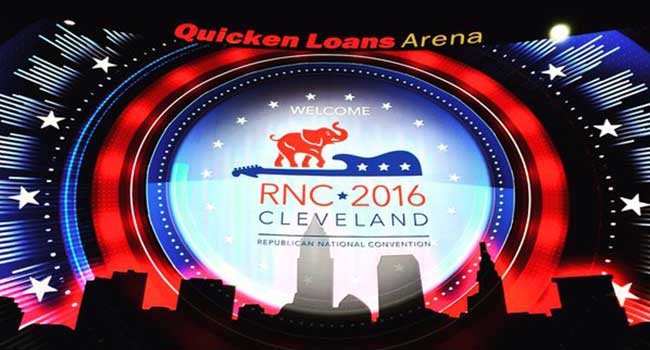
Cleveland is spending $20 million in federal money on riot and security gear for the Republican Convention.
- By Sydny Shepard
- Apr 14, 2016

Protesters who’ve occupied a federal building in Oregon have been arrested.
- By Sydny Shepard
- Jan 27, 2016
New Samsung WiseNet Camera App records directly to disk.

Nearly every major U.S. carrier won’t let you board with a hoverboard in tow.
- By Sydny Shepard
- Dec 14, 2015

In the weeks following the massive explosion at a warehouse owned by Ruihai International Logistics in the Chinese port of Tianjin, investigators are getting a better idea of what led to the disaster that killed 173 people—104 of whom were firefighters—and injured hundreds more.
- By Glenn Trout
- Dec 01, 2015

Traditionally, electrical substation security was aimed only at preventing access to stop vandalism and improve safety. Today, however, security efforts have been redefined to address new threats in order to protect critical infrastructure.
- By Reinier Tuinzing
- Dec 01, 2015
STANLEY Security and I-View announce their partnership for live, actionable verified alarm response system.

To support safety and notify personnel in the case of an emergency, Peru LNG’s needed a general alarm and mass notification system (MNS).
- By Marla Moran
- Aug 26, 2015

Mitigate insider threat and improve perimeter security and personnel assurance to ensure only trusted resources have access.
- By Daniel W. Krantz
- Jul 09, 2015